In the rapidly evolving world of mobile development, cross-platform frameworks like Flutter and React Native have become a widely adopted choice for efficiency. They offer the dream of “write once, run anywhere,” allowing businesses to deploy feature-rich applications to both iOS and Android from a single codebase. However, this architectural convenience often introduces a complex, hidden layer of security vulnerabilities that traditional protection methods fail to address.
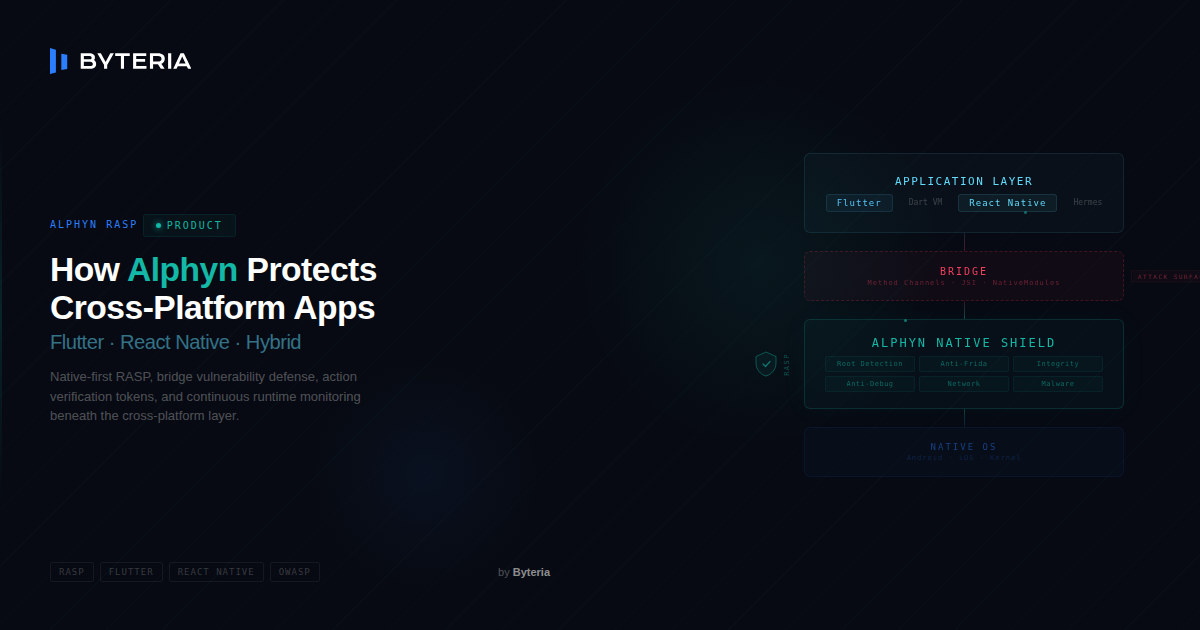
While developers focus on the UI and business logic residing in Dart or JavaScript, they often overlook the critical “bridge” that connects their code to the native operating system. This bridge, and the runtime environment it lives in, is where the most sophisticated attacks occur today.
The Cross-Platform Security Gap: Where Traditional Solutions Fail
Cross-platform apps are unique beasts. They aren’t just native binaries; they are hybrids that bundle a runtime (like the Flutter Engine or Hermes JS engine) along with your application assets. This structure creates specific attack vectors that are often easier to exploit than those in purely native apps.
1. The “Bridge” Vulnerability: A Highway for Attackers
The most critical component of any cross-platform app is the communication bridge. Every time your Flutter or React Native code needs to perform a sensitive action (like storing a token, accessing the GPS, or making a payment request), it sends a message across this bridge to the native Android or iOS layer.
Attackers know this. By using dynamic instrumentation tools like Frida, they can “hook” into this bridge. They can:
- Intercept Traffic: Read sensitive data (PII, API keys) as it passes from the secure native layer to the exposed JS/Dart layer.
- Manipulate Payloads: Modify a payment request from $100.00 to $1.00 before it hits the native payment SDK.
- Bypass Validation: Spoof a “Success” response from a security check, fooling the app into thinking it’s running in a safe environment.
2. Logic Exposure and Reverse Engineering
There is a dangerous myth that compiling to native code makes an app secure.
- React Native: Ships with a JavaScript bundle. Even if minified, this logic is easily extracted and deobfuscated, revealing your API endpoints, encryption keys, and business logic flow.
- Flutter: While AOT compilation raises the bar, attackers can still recover meaningful logic via static and dynamic analysis (strings, API routes, protocol structures, and control flow graphs) without needing niche tools.
3. Runtime Blind Spots
Many security libraries for these platforms are essentially wrappers around native logic, but they are initialized too late. If your security check runs in JavaScript after the app has loaded, an attacker running in a manipulated environment (like a rooted device or emulator) has already had time to bypass your checks or hook your initialization routines.
Alphyn’s Solution: A Native Shield for Hybrid Apps
Alphyn takes a fundamentally different approach. We don’t just protect the JavaScript or Dart layer; we secure the Native Runtime Environment that supports it. By operating in the native iOS/Android layer, beneath the Flutter/RN runtime inside the app process, Alphyn provides a defense-in-depth strategy that is invisible to the higher level code but much harder to bypass reliably.
Step-by-Step Protection Lifecycle
Here is how Alphyn secures your application from launch to sensitive action:
Step 1: Early Initialization & Continuous Assessment (The 6 Core Modules)
As your app initializes, Alphyn’s native engine engages its 6 Core Protection Modules (or just enabled ones as your dashboard config) to assess the device’s security posture. This isn’t just a simple check; it’s a comprehensive audit:
- Root & Jailbreak Detection: Identifying compromised OS environments where system security guarantees are void.
- Emulator Detection: Flagging synthetic devices and simulators often used by bot farms to automate attacks.
- Runtime Protection: Detecting dynamic instrumentation tools (like Frida) and hooking frameworks that try to manipulate your app’s memory in real-time.
- Tampering Detection: Verifying the app’s code signature and integrity to ensure the binary hasn’t been modified or repackaged.
- Malware & Suspicious App Detection:
- Android: Scanning for known malicious packages and abuse of accessibility services.
- iOS: Detecting indicators of compromise, injected dylibs, and suspicious runtime states.
- Network Protection: Validating the integrity of the connection, detecting unsecured proxies, and preventing Man in the Middle (MITM) attacks.
If any of these modules report a critical violation, Alphyn can block the app from initializing entirely (or follow your custom rules as configured in the dashboard), preventing your sensitive code and API keys from ever being loaded into memory.
Step 2: Continuous Runtime Monitoring (RASP)
Security isn’t a one time check. Attackers often launch tools after the app has started. Alphyn runs continuously in the background, re-evaluating all modules in real-time. This means it can detect threats that emerge mid session:
- Debugger Attachment: Detecting if someone tries to attach a debugger to step through your code after launch.
- Dynamic Analysis: Identifying if Frida or a hook is injected while the app is running.
- Network Changes: Catching a user who enables a malicious proxy or VPN after logging in.
- Malware Installation: Flagging a suspicious app that is installed or updated while your session is active.
(Note: Alphyn uses lightweight periodic checks and event-driven triggers to minimize overhead.)
Step 3: Action Verification (The “Certificate of Health”)
This is the game-changer for cross-platform apps. When a user performs a high risk action (e.g., “Transfer Money” or “Change Password”), you shouldn’t just trust the request coming from the app.
- Request: The app asks Alphyn for a verification token.
- Attestation: Alphyn performs an instant, deep health check of the device and app integrity.
- Token Generation: If safe, Alphyn generates a cryptographic, short-lived token.
- Backend Validation: Your backend server receives this token along with the user’s request. It validates the token with Alphyn’s cloud. If the token is missing or invalid, your backend rejects the request immediately.
This effectively neutralizes “Bridge” attacks, even if an attacker spoofs the request, they cannot forge the cryptographic proof of a healthy device.
Dynamic Defense: The Alphyn Dashboard & Rule Models
Security needs to move as fast as attackers do. Hardcoding security logic (e.g., if (isRooted) exit()) is brittle and requires an App Store update to change. Alphyn empowers you with Dynamic Rule Models managed via our dashboard.
- Real-Time Policy Updates: Decide instantly how your app should respond to threats.
- Scenario: You decide to customize protection for a specific rollout or testing phase. You can disable a specific module instantly via the dashboard, giving you full control without needing a new App Store submission.
- Scenario: You want to be alerted immediately when a high-risk threat (like a rooted device) is detected. Alphyn can send a real-time notification via Webhooks, Slack, Teams, WhatsApp or Telegram.
- Scenario: Under a severe attack, you can configure the policy to crash the app immediately upon detection of a specific threat, stopping the attacker in their tracks.
- Granular Threat Responses:
- Monitor: Log the threat but allow the user to continue (useful for gathering intelligence).
- Flag: Mark the user’s session as “High Risk” for your fraud team to review.
- Block: Crash the app or show a blocking screen to prevent access.
- Threat Intelligence: Visualize where attacks are coming from. Access wide-range analytics on the dashboard, covering everything from “Rooted Devices” to “Proxy Usage” to fully understand your threat landscape.
Who Needs This Protection? (Target Use Cases)
In today’s interconnected ecosystem, the need for robust security extends beyond niche industries. Basically, every app accessible from any app store needs protection. Whether it’s a simple utility or a complex enterprise tool, every application interacts with APIs, manages local databases, and relies on code integrity to function correctly. Protecting these assets is not just about compliance; it’s about maintaining user trust and preventing data leakage.
Fintech & Banking
- Concern: Man in the middle attacks, credential stuffing, transaction tampering.
- Alphyn Value: Action Verification ensures that every transaction originates from a genuine, untampered app on a secure device.
Healthcare & MedTech (HIPAA)
- Concern: Leakage of Patient Health Information (PHI) via compromised devices or insecure storage.
- Alphyn Value: Robust Root and Jailbreak detection ensures that PHI is never accessed or processed on a compromised device where standard encryption keys can be easily extracted.
Alignment with OWASP Mobile Top 10 (2024)
Alphyn provides comprehensive coverage across the entire spectrum of mobile risks identified by OWASP:
- M1: Improper Credential Usage: By detecting compromised environments (Root/Jailbreak) and runtime hooking tools (Frida), Alphyn prevents attackers from harvesting credentials from memory or intercepting them during login.
- M2: Inadequate Supply Chain Security: Alphyn’s App Integrity checks verify the binary’s cryptographic signature, ensuring that the app installed on the user’s device is exactly what you published, protecting against repackaged or “modded” apps.
- M3: Insecure Authentication/Authorization: Action Verification adds a critical layer of defense, ensuring that sensitive requests (like password changes) originate from a healthy, untampered app session, preventing session riding or replay attacks.
- M4: Insufficient Input/Output Validation: Alphyn complements backend validation by verifying the integrity of the request source via Action Verification, ensuring that payloads from a compromised environment are rejected.
- M5: Insecure Communication: Alphyn secures the channel between your app and its backend, detecting MITM attacks and ensuring certificate validity.
- M6: Inadequate Privacy Controls: By detecting malware and suspicious file paths, Alphyn helps protect user privacy by identifying unauthorized apps or scripts that might attempt to harvest PII or monitor user activity.
- M7: Insufficient Binary Protections: Our core RASP features (Anti-Debug, Anti-Tamper) make reverse engineering significantly more difficult and expensive for attackers.
- M8: Security Misconfiguration: Alphyn immediately flags if a production app is running in a debuggable state or if developer options are enabled on a high-risk device.
- M9: Insecure Data Storage: By detecting compromised environments (Root/Jailbreak), Alphyn prevents sensitive data from being stored on devices where the OS-level sandbox and keychain protections are broken.
- M10: Insufficient Cryptography: Alphyn handles its own cryptographic operations for Action Verification and secure communication, ensuring that critical security functions rely on well-reviewed, standard algorithms and proper key management.
What Alphyn Does in 60 Seconds
- Native-First: Initializes in the iOS/Android layer to detect threats before your app’s main logic takes over.
- Continuous RASP: Monitors the environment in real-time for debuggers, hooking (Frida), and tampering—not just at launch.
- Action Verification: Generates a cryptographic proof-of-health token for sensitive actions, allowing your backend to reject requests from compromised devices.
How it Integrates (Flutter Example)
1. Flutter Implementation:
// main.dart
import 'package:alphyn_sdk/alphyn_sdk.dart';
void main() async {
WidgetsFlutterBinding.ensureInitialized();
// Initialize native security layer
await AlphynSdk.initialize(interval: 45.0);
runApp(const MyApp());
}
// Inside your payment logic
Future<void> sendPayment(double amount) async {
// Get a health token for this action
final verification = await AlphynSdk.verifyAction(
actionLabel: 'payment_transfer',
context: {'amount': amount.toString()}
);
if (verification.success) {
// Send token to backend
await backend.processPayment(amount, verification.token);
} else {
// Handle security rejection (e.g., device is rooted)
showError("Security check failed: ${verification.errorMessage}");
}
}
2. Backend Validation:
// backend/payment_route.js
async function handlePaymentRequest(req, res) {
const { amount, alphynToken } = req.body;
// Verify the token with Alphyn Cloud
const isSecure = await alphyn.verifyToken(alphynToken);
if (!isSecure) {
return res.status(403).json({ error: "Request from compromised device rejected." });
}
// Proceed with payment...
}
Conclusion
Cross-platform speed shouldn’t mean cross-platform exposure. Alphyn starts in the native layer before your Dart/JS runtime is fully active, continuously monitors for tampering and instrumentation, and lets your backend require cryptographic proof of device/app health for high-risk actions. Instead of trusting the bridge, you verify the environment behind it.
Don’t leave your bridge undefended. Secure it with Alphyn.
Built-in defense
Runtime threats require runtime protection.
Alphyn is a powerful SDK that defends against reverse engineering, tampering, and runtime attacks—all with effortless integration and enterprise-grade security.